ShadowRay 2.0: AI-Powered Cyberattack Exposed
ShadowRay 2.0 Cyberattack
A sophisticated cyber operation known as ShadowRay 2.0 is actively compromising publicly accessible Ray clusters through the exploitation of a previously disclosed code execution vulnerability, transforming these systems into a self-replicating cryptocurrency mining network.
Ray, an open-source framework created by Anyscale, enables developers to construct and expand AI and Python-based applications across distributed computing environments structured as clusters or head nodes.
Security analysts at Oligo, a runtime security firm, have identified a malicious actor designated as IronErn440 who is leveraging artificially intelligence-generated attack code to breach vulnerable Ray infrastructure exposed to the public internet.
The researchers emphasize that these intrusions extend far beyond simple cryptocurrency mining operations, encompassing activities such as credential harvesting, data exfiltration, and the deployment of distributed denial-of-service (DDoS) capabilities.
This latest ShadowRay 2.0 operation represents a continuation of an earlier ShadowRay offensive, which Oligo previously documented as occurring between September 2023 and March 2024.
Oligo's investigation revealed that both attack campaigns exploited CVE-2023-48022, a critical security flaw that remains unpatched. The vulnerability was left unaddressed because Ray's architecture was originally intended for deployment within trusted environments characterized as "strictly-controlled network environments."
Despite this design assumption, researchers have discovered an alarming reality: over 230,000 Ray servers are currently accessible via the internet, representing a dramatic escalation from "the few thousand we observed during our initial ShadowRay discovery."
In their latest analysis published today, Oligo documented two distinct attack phases. The first wave utilized GitLab infrastructure for malicious payload distribution and concluded on November 5, while the second wave, which began on November 17 and remains active, exploits GitHub for the same purpose.
Security researchers at Oligo have determined that malicious code deployed during these intrusions bears telltale signs of artificial intelligence assistance in its creation. The determination stems from examining how the code was structured, reviewing embedded annotations, and studying the methods used for managing errors.
When analysts decoded one particular malicious package, they discovered it included documentation strings alongside unnecessary echo commands. These characteristics point strongly toward the involvement of large language models in producing the attack code.
The presence of such elements provides compelling evidence that threat actors are now leveraging AI-powered tools to streamline the development of their exploitation frameworks and cryptocurrency mining payloads.Attackers are exploiting CVE-2023-48022 to submit malicious tasks through Ray's unauthenticated jobs API. These tasks execute multi-stage bash and python payloads, hijacking the platform's orchestration to deploy malware across every node in a cluster. This method enables the threat to spread autonomously from one compromised cluster to another. The deployed crypto-mining module itself exhibits signs of being AI-generated. It performs reconnaissance, checking available CPU and GPU resources and the level of system access. Code within the payload reveals the attacker's preference for systems with at least eight cores and root privileges, humorously labeling such a setup "a very good boy." For the mining operation, the attackers employ XMRig to mine Monero. To avoid triggering immediate alerts, the malware is configured to use only 60% of the available processing power. The miners are strategically placed in deceptive file locations and masquerade under innocuous process names, such as 'dns-filter,' to evade detection. Persistence is ensured through the creation of cron jobs and modifications to systemd. A notable aspect of this campaign is the attacker's territorial behavior on compromised infrastructure. They actively seek out and terminate any rival cryptocurrency mining scripts already running on the cluster. Furthermore, they block connections to other mining pools by manipulating the `/etc/hosts` file and configuring iptables firewall rules. 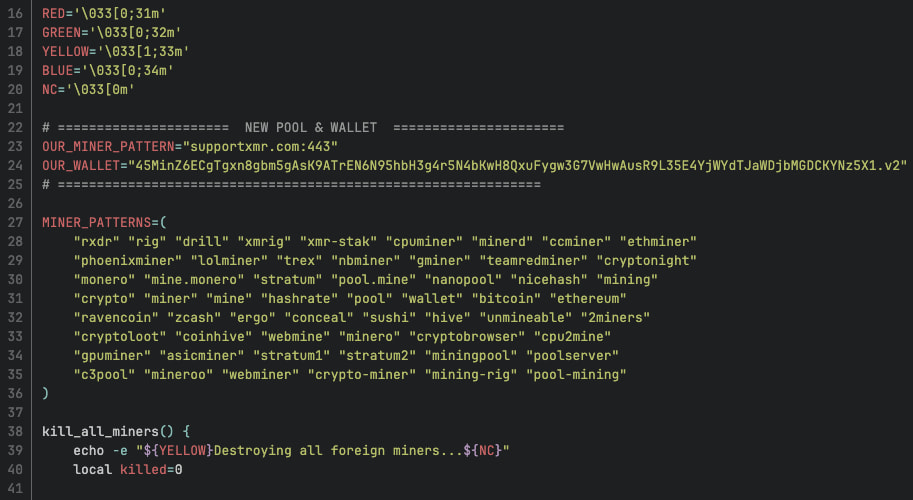 ### Malware and Security Risks The malicious software not only facilitates cryptocurrency mining but also establishes several Python-based reverse shells connecting back to the attacker's servers. This setup grants the intruder interactive access to the compromised system, enabling them to extract sensitive information such as workload environment details, MySQL login credentials, proprietary AI models, and source code stored within the cluster. In addition, the malware is capable of conducting distributed denial-of-service (DDoS) attacks by leveraging the sockstress tool. This tool targets resource asymmetry by creating numerous TCP connections through raw sockets, overwhelming the targeted network. Analysis of the cron jobs created by the attacker reveals a scheduled task running every 15 minutes. This script routinely checks a GitHub repository for new payload updates, ensuring the malware remains up-to-date and adaptable to evolving attack strategies. 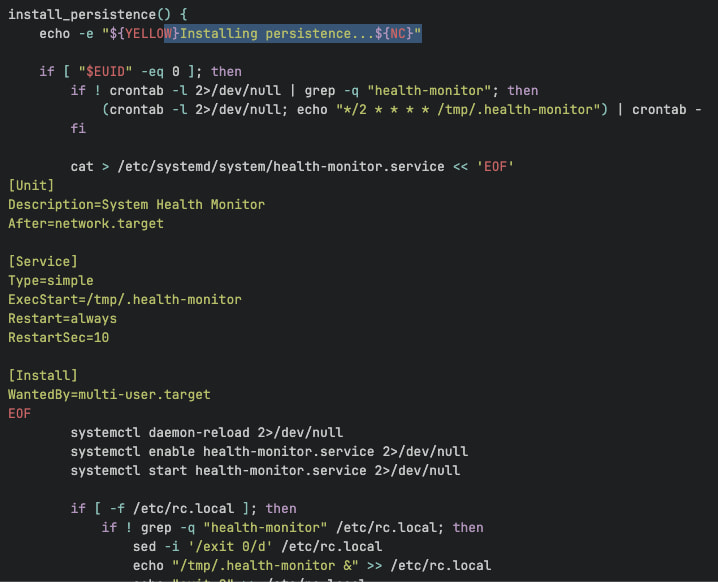 Since no patch is available for CVE-2023-48022, deploying Ray clusters requires strict adherence to vendor best practices. Anyscale has reiterated key security recommendations following the initial ShadowRay campaign discovery, emphasizing the need for a secure and trusted deployment environment. It is essential to shield clusters with firewalls and enforce strict security group policies against unauthorized entry. Furthermore, applying authorization controls to the Ray dashboard port—default 8265—is advised, along with continuous monitoring of AI clusters to swiftly detect any abnormal behavior. ### Why People Need VPN Services to Unblock Porn Many individuals turn to VPN services to [unblock porn](https://www.safeshellvpn.com/unblock/porn?utm_source=blog) when they encounter geographical restrictions, government censorship, or network-level blocks that prevent them from accessing adult websites in their region. By routing internet traffic through encrypted servers in different locations, VPNs enable users to circumvent these barriers while maintaining privacy and anonymity from ISPs and surveillance systems. Porn unblocked refers to the ability to access adult content that would otherwise be restricted or censored, achieved through technologies like VPNs that mask user locations and bypass filtering mechanisms imposed by governments, workplaces, or internet providers. ### Why Choose SafeShell VPN to Access Adult Content If you're seeking a reliable solution to [unblock porn sites](https://www.safeshellvpn.com/unblock/porn?utm_source=blog) and access region-restricted adult content, SafeShell VPN emerges as an excellent choice worth considering. This premium service delivers numerous advantages that make it particularly well-suited for users who prioritize both privacy and performance. Here's what makes SafeShell VPN stand out: 1. SafeShell VPN provides exceptional connection speeds that eliminate the frustrating lag and buffering issues commonly associated with other VPN services, ensuring smooth streaming of high-quality adult content without interruptions. 2. The unique App Mode functionality allows simultaneous access to content from different geographical regions, giving you the flexibility to explore diverse platforms without the inconvenience of constantly changing server locations. 3. With the proprietary ShellGuard protocol, your browsing activities remain completely private and secure, effectively protecting you from monitoring by internet service providers, network administrators, and other third parties who might attempt to track your online behavior. 4. SafeShell VPN offers comprehensive multi-device compatibility, supporting up to five simultaneous connections across various platforms including smartphones, tablets, computers, and smart TVs, ensuring consistent protection regardless of which device you're using. 5. The extensive global server network enables effortless bypassing of geographical restrictions, granting you access to adult content that might otherwise be unavailable in your current location while maintaining optimal performance throughout your browsing session. ### How to Use SafeShell VPN to Unlock Porn Sites To begin using [SafeShell VPN](https://www.safeshellvpn.com/?utm_source=blog) for viewing region-restricted adult content, start by subscribing to SafeShell VPN through their official website at [https://www.safeshellvpn.com](https://www.safeshellvpn.com/?utm_source=blog)/. Choose a plan that suits your browsing needs and complete the registration process. After subscribing, download and install the SafeShell app on your preferred device(s), ensuring you have the correct version compatible with your operating system. Once installed, launch the application and enable the App Mode feature, which provides enhanced access and flexibility for browsing. Next, browse through the available server locations and select a region where the desired content is accessible. Connecting to this server will mask your real IP address and make it appear as though you are browsing from the selected region. Finally, start browsing your favorite adult sites with complete privacy and unrestricted access, knowing your identity remains protected throughout the process.
- Nghệ thuật
- Khóa Học
- Thủ công mỹ nghệ
- Nhảy
- Đồ uống
- Phim ảnh
- Ngoại Hình
- Đồ ăn
- Games
- Làm vườn
- Sức khỏe
- Nhà
- Văn học
- Âm Nhạc
- Kết Nối
- Buổi tiệc
- Tôn giáo
- Mua Sắm
- Thể Thao
- Nhà hát
- Khác